Overview
The most secure way to login to a remote machine and copy files to and from it, is by using SSH keys (normally RSA).Managing these keys, between multiple servers and especially between development machines can become cumbersome. There is also the security threat of leaving keys lying around on machines.
A great way to not have keys as files on local disk is using the unix ssh-agent program. Tools like ssh, rsync and scp read from the ssh-agent when trying to access a server, and will try each key until a valid key is found. This happens quickly and delays trying keys are not observable to a user.
The
pk ssh-add command is used to download any ssh keys securely and add them to the local running ssh-agent.
After which you can run ssh, rsync or scp normally and the ssh-agent will make the key available to them.
E.g
pk ssh-add -s personal -n mykey,myclient-key1 -p
ssh-add -D
Formats and Types
Keys must be PEM encoded, and can be RSA (PKCS1, or PKCS8) or ECDSA. Keys can also be password protected themselves. When thepk ssh-add command reads a password protected key,
it will prompt for the key's password, to decrypt it for the ssh-agent.
Requirements
We assume you have:Use case
We are going to walk you though an example where we setup an AWS server with a private RSA key. We'll add this key to our pkhub "Pub/Priv Keys", and show you how to run thepk ssh-add
command to add this key to the local ssh-agent. Finally we'll show how to ssh into the AWS server
using the ssh-agent.
Here we use AWS, but this can be applied to any cloud provider and or any self managed servers, even your local dev laptops.
Step 1: Setup
-
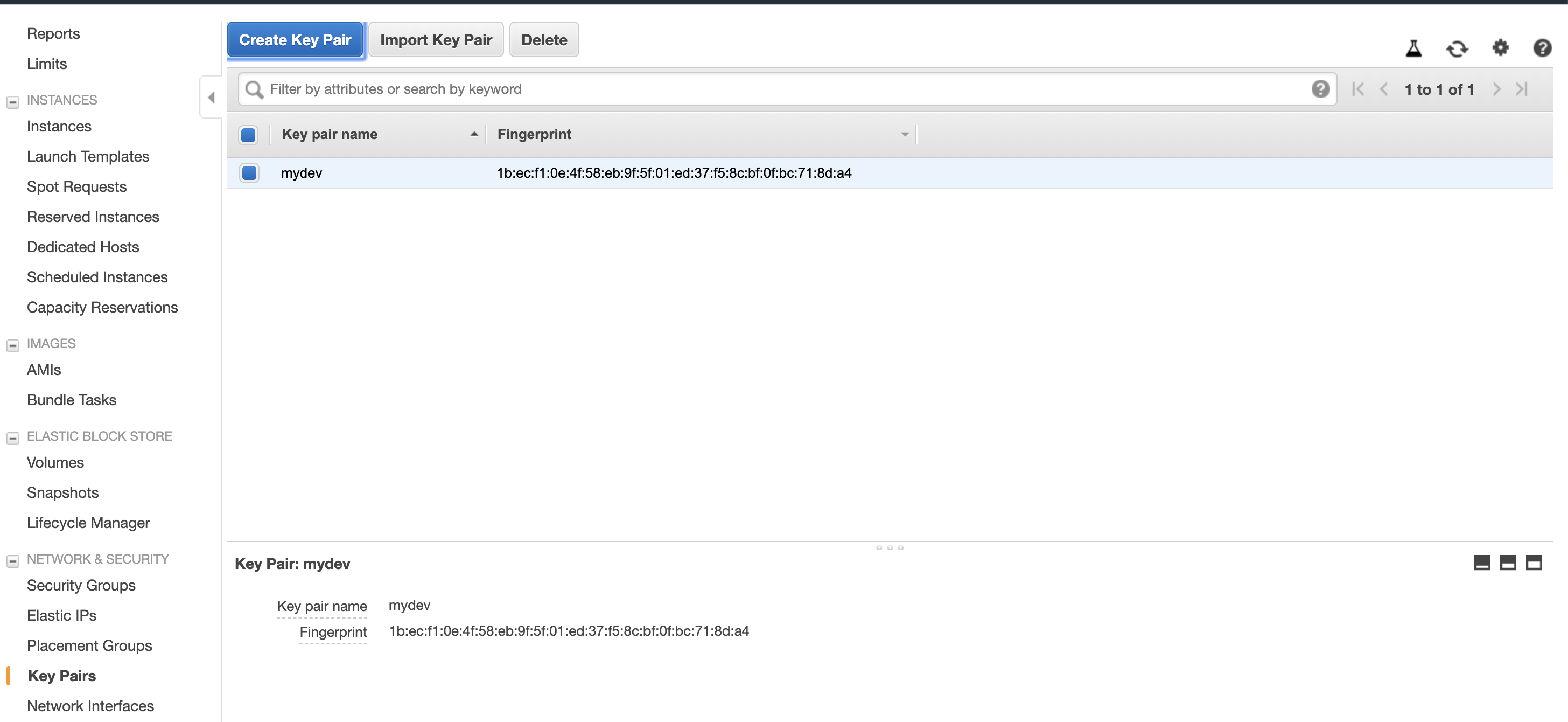
Create the key in AWS
-
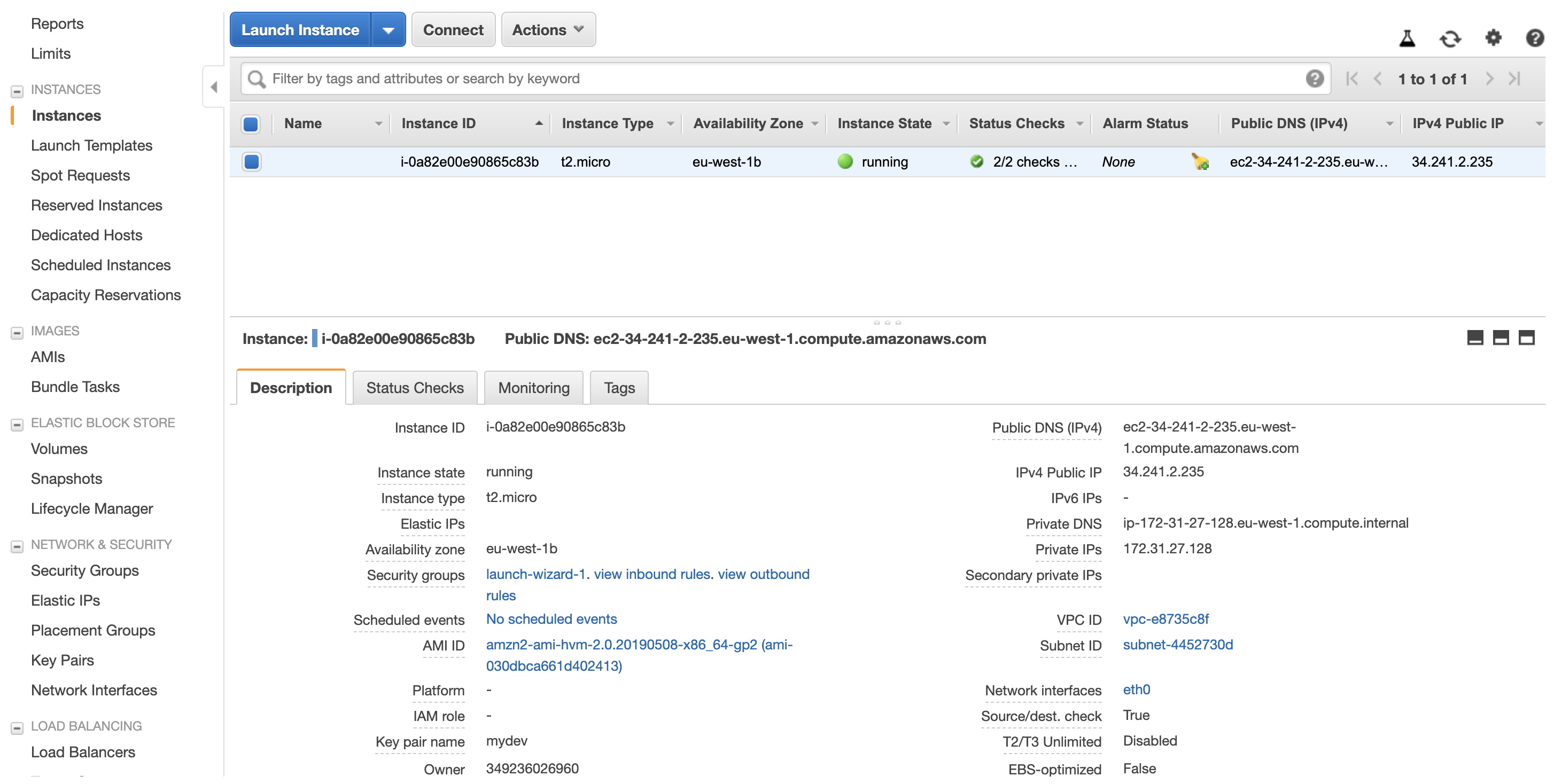
Create the aws server, with the ssh key assigned
-
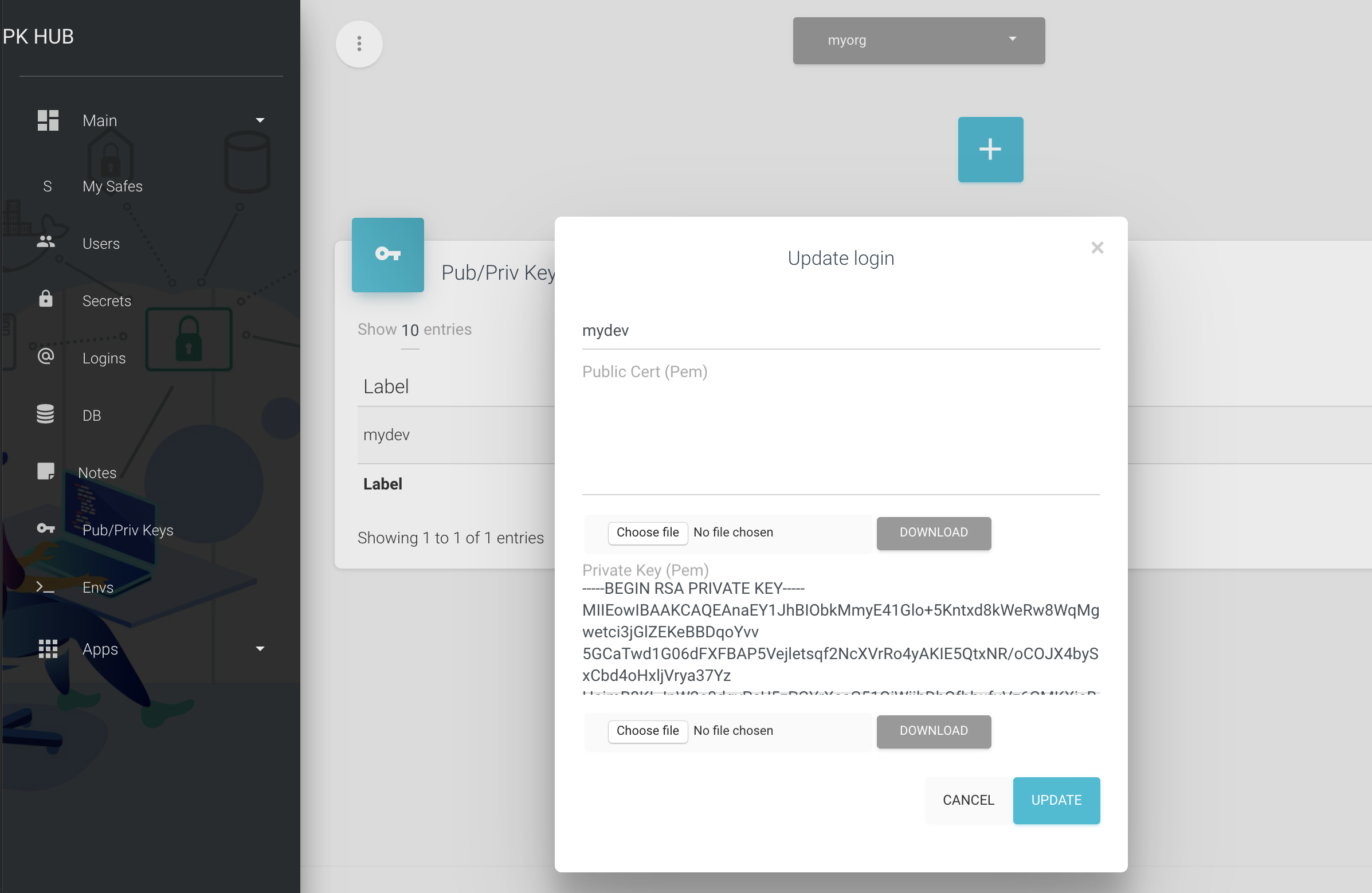
Create the PK Hub Pub/Priv Key entry
Step 2: Run the pk ssh-add command
You can now add the private key using the PK CLI. Thepk ssh-add" command can download any private keys from your pkhub safe and add it to the local ssh agent.
pk shh-add -s myorg -n mydev -p
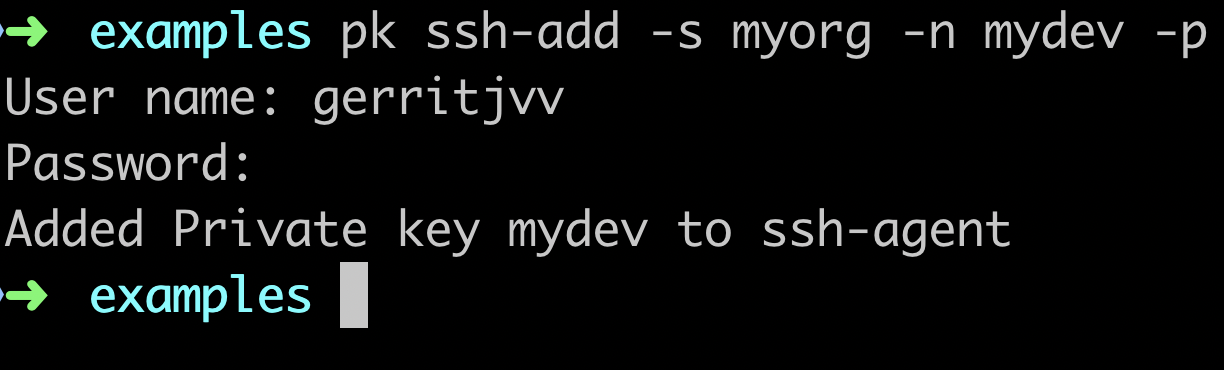
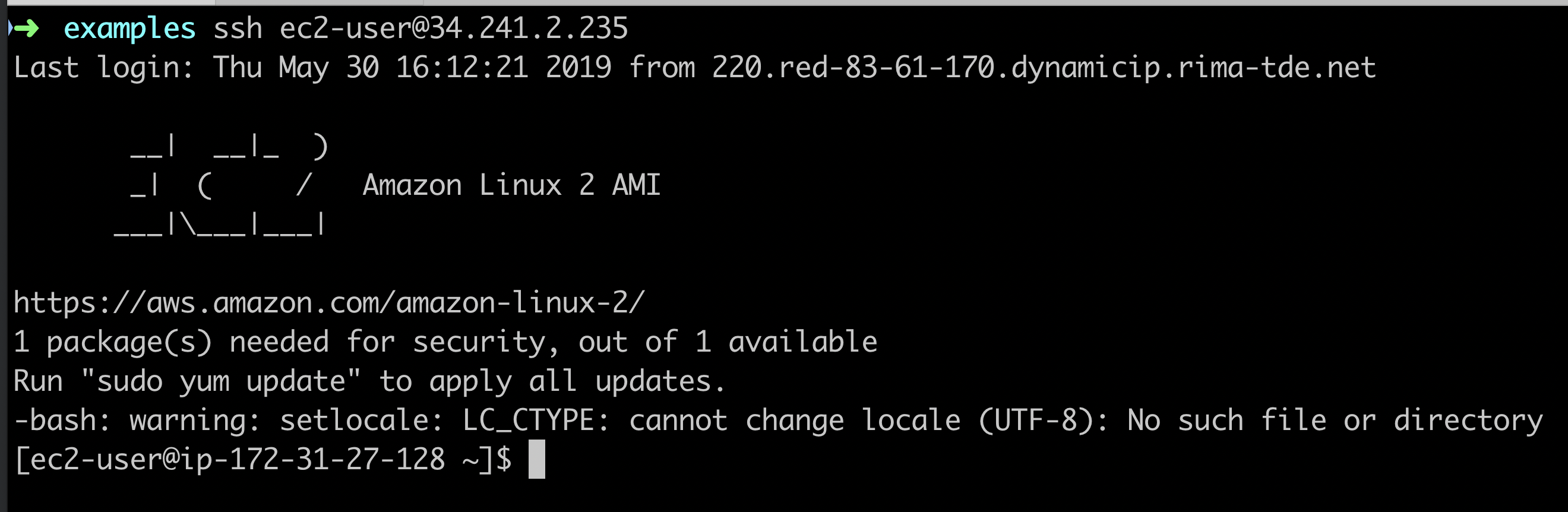
Step 3: SSH into the server